Manage Policy
Smart Policy. Built to Scale.
Automate and enforce secure, compliant access through your policy database, so you achieve dynamic security that scales with your enterprise.
Build Dynamic Policies with Velotix
Velotix learns from how your teams grant access by analyzing current behaviors, user roles, and data use to generate adaptive policies that reflect real-world decisions. These policies automatically evolve with organizational changes and new data, minimizing manual upkeep while keeping access secure and compliant.
Real Business Success
Fewer Costly Breaches
More Scalable Policy Coverage
Lower Operational Overhead
Less Audit Prep Time
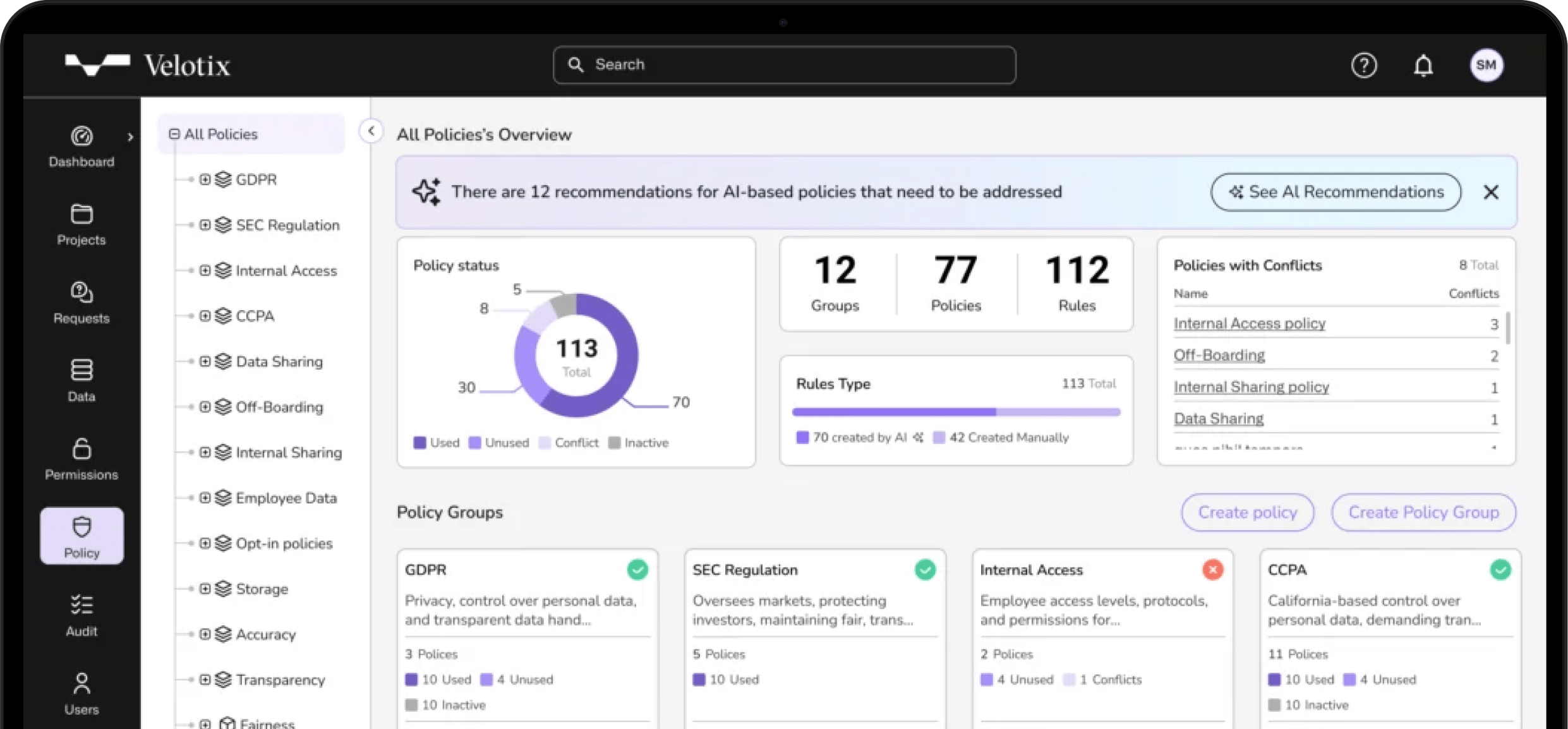
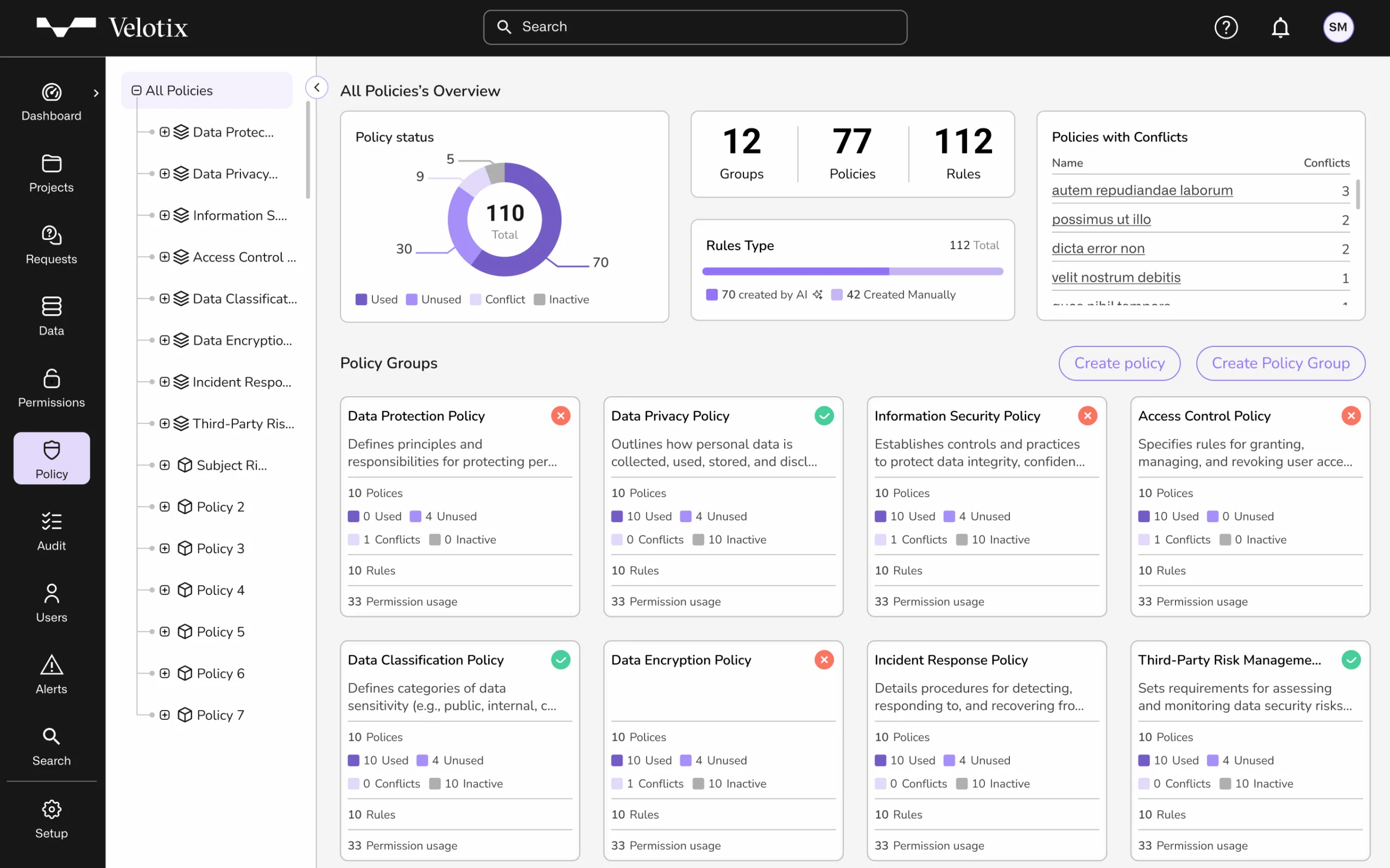
Create a Single Source of Truth
Align Policies
Gather all your access rules, compliance requirements, and security policies into one unified platform.
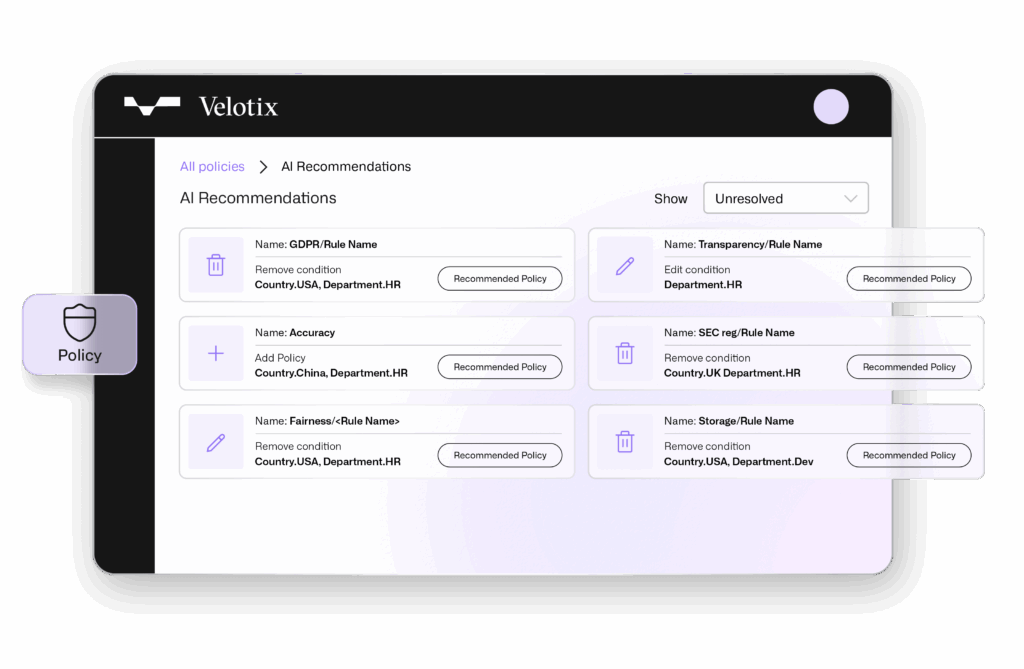
Policy Recommendations
Respond faster to access requests and regulatory changes, so you minimize errors, and secure sensitive information.
Centralized Policy Hub
Bring all your access rules, compliance requirements, and security policies together.
Align Policies in Real Time
Regulations like GDPR, HIPAA, and CCPA are constantly evolving — and so are your data needs. Velotix continuously learns from your environment and adapts policies in real time, ensuring access stays aligned with internal governance, data sensitivity, and evolving compliance obligations.
Unlock Dynamic Security
By detecting anomalies like excessive usage, irregular hours, or atypical retrieval, enforcing secure access and helping prevent compliance violations or unauthorized data exposure.
Automate Policy Management
Reduce the burden on approvers and data requesters by automating policy management fueling team innovation, reducing operational overhead, and ensuring compliance across your data landscape.
Policy Recommendations
Make data access decisions based on crystal clear Policy Recommendations and build your policy database based on past approvals.
Grant or Deny Access Faster
Make confident decisions within context—user roles, data sensitivity and usage history are all presented in one place, so you can make faster, informed decisions.
Turn Decisions into Policy
Convert approved requests into scalable, compliant rules that grow with your organization.
Scale with Confidence
Velotix continuously adapts to evolving regulations, updating your policy database in real time so you’re free to expand without compromising compliance.
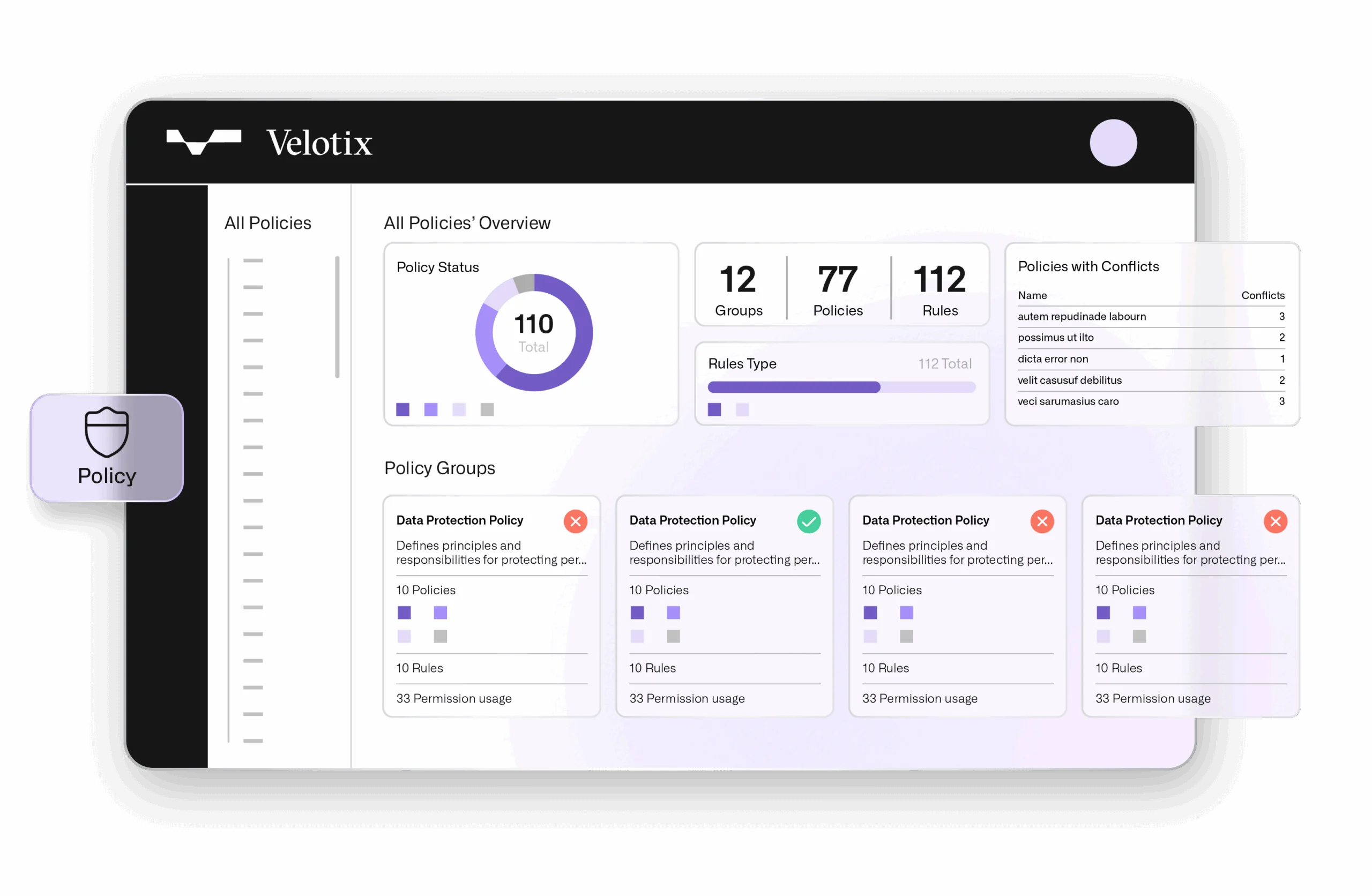
Finally, A Centralized Policy Hub
Simplify data governance with a centralized policy hub that brings all your access rules, compliance requirements, and security policies together. With a Centralized Policy Hub, improve visibility, reduce complexity, and support secure, consistent enforcement across your entire data ecosystem.

Velotix is the missing PBAC brain for the modern data stack.
GARTNER ANALYST
Your Holy Grail of Policy Is Here
See how Velotix helps you eliminate manual work and enforce compliant access at scale.