What is Unstructured Data Security?
Unstructured data security is an organization’s practices and technologies for safeguarding and managing its unstructured data, including documents, emails, images, and multimedia files. It relies on well-defined unstructured data governance strategies to ensure proper access controls, data classification, and retention policies. Unstructured data protection uses techniques like encryption, data loss prevention, and backup solutions to mitigate data security risks such as data breaches, unauthorized access, and accidental data deletion. Proactively managing unstructured data security ensures businesses maintain data integrity, comply with regulations, and minimize the potential for data misuse or exposure.
Characteristics of Unstructured Data
Unstructured data describes information that doesn’t follow a predefined model or format. Because it doesn’t fit neatly into rows and columns, it’s often difficult to analyze and process. Key characteristics of unstructured data include:
- Lack of structure. It’s challenging to extract or analyze insights using traditional data management tools.
- Varied formats. It can come in various formats, such as text documents, emails, social media posts, images, videos, and audio recordings.
- Human-generated. A significant portion of it is generated by humans, making it more complex and diverse.
- Difficult to process. It typically requires advanced techniques, such as natural language processing (NLP), to extract meaningful information.
- Large volumes. The rise of digital technologies and the internet has led to significant growth in the volume of unstructured data organizations generate, creating challenges for storage and processing.
In a world where unstructured data makes up a significant portion of the data landscape, businesses must find ways to effectively manage and analyze it to unlock its potential value. Embracing new technologies and techniques is crucial to extracting the valuable insights hidden within this vast and diverse pool of information.
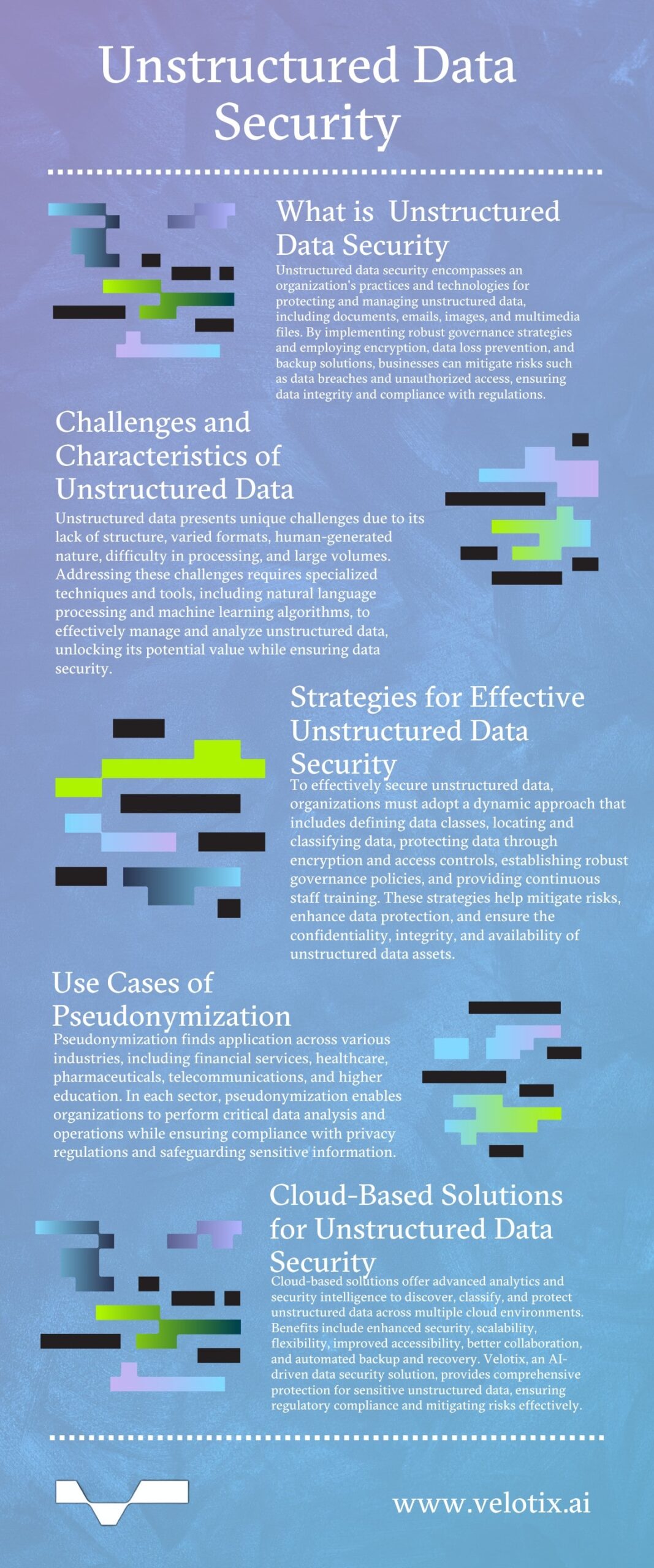
Challenges in Securing Unstructured Data
Unstructured data’s inherent complexity and lack of structure make securing it uniquely challenging. For instance, unstructured data discovery presents a major hurdle, as the data is often scattered across various locations, making it much harder to identify and classify sensitive information. Unstructured data classification is another obstacle, as traditional data classification methods are generally not as effective for unstructured formats like emails, documents, and multimedia files.
Unstructured data processing often requires specialized techniques and tools, including NLP and machine learning algorithms, to extract meaningful insights and information, adding an extra layer of complexity to data security efforts.
Unstructured data also poses a significant challenge in cloud data security, as it becomes more difficult to identify and protect sensitive data assets that might be embedded within unstructured formats. Unlike structured databases, where sensitive information is typically well-defined and contained within specific fields, unstructured data frequently contains sensitive information scattered throughout its content, making it harder to discover and secure.
To overcome these and other obstacles, organizations must adopt a dynamic and multifaceted approach to unstructured data management that strikes a balance between accessibility and security while effectively managing and protecting unstructured data assets, including:
- Developing specialized strategies tailored to each issue.
- Creating an adaptable data management framework capable of seamlessly handling the ever-changing nature of unstructured data.
- Investing in advanced data security tools.
- Enhancing data governance policies.
- Providing continuous staff training.
Strategies for Unstructured Data Security
Implementing effective unstructured data security strategies is crucial to safeguarding sensitive information and maintaining compliance. Essential approaches include:
- Defining data classes based on sensitivity levels.
- Locating and classifying unstructured data across the organization using advanced data discovery tools.
- Protecting data through encryption, access controls, and data loss prevention measures.
Establishing robust data governance policies, implementing data retention and disposal protocols, and providing regular security awareness training to employees are also essential components of any data security program. By proactively addressing these areas, organizations can mitigate risks, enhance data protection, and ensure the confidentiality, integrity, and availability of their unstructured data assets.
Cloud-Based Solutions That Protect Unstructured Data
Cloud-based solutions for securing unstructured data use advanced analytics to discover, classify, and protect unstructured data across multiple cloud environments, ensuring consistent security policies and controls. Benefits include:
- Enhanced security. Cloud-based security solutions offer advanced threat protection, employing the latest technologies and security intelligence to safeguard unstructured data from cyber threats such as malware, ransomware, and data breaches. They provide robust encryption, access controls, and data loss prevention measures to ensure data confidentiality and integrity and, more often than not, provide a higher level of protection than many on-premises solutions.
- Scalability. Cloud solutions scale seamlessly, allowing organizations to accommodate growing volumes of unstructured data without the need for significant upfront investments in hardware and infrastructure. This scalability ensures an organization’s data security measures can keep pace with its growing data needs, providing consistent protection as data volumes increase.
- Flexibility. Cloud-based solutions offer flexibility in deployment models, meaning organizations can choose between public, private, or hybrid cloud architectures based on their specific security and compliance requirements. This flexibility enables enterprises to tailor their unstructured data security strategies to their unique needs, ensuring optimal protection while maintaining operational efficiency.
- Improved accessibility. Cloud solutions enable secure access to unstructured data from anywhere, facilitating remote work and collaboration among dispersed teams. Powerful access controls and encryption ensure data remains protected while enabling authorized users to access and share information securely, fostering productivity and efficient workflows.
- Better collaboration. Advanced cloud-based solutions integrate with collaboration tools and platforms, enabling secure sharing and collaboration on unstructured data assets, streamlining workflows, and improving communication. This reduces the risk of data leaks or unauthorized access during collaborative processes involving unstructured data.
- Automated backup and recovery. Cloud providers typically provide the latest in backup and disaster recovery solutions, ensuring unstructured data is regularly backed up and can be quickly recovered in the event of data loss or system failures. This automated backup and recovery process minimizes downtime, data loss risks, and the associated business impact, providing organizations with greater resilience and business continuity.
Organizations that invest in AI-driven cloud-based data security solutions achieve higher levels of protection for their unstructured data. Velotix is a groundbreaking data security solution that safeguards sensitive information contained in unstructured data, ensuring regulatory compliance and providing comprehensive data governance and risk mitigation capabilities.