Investing in technologies that ensure data confidentiality and integrity is one of most effective ways for organizations to instill stakeholder trust and demonstrate a commitment to data security. Pseudonymization is a common data anonymization technique for obfuscating sensitive information while preserving data usefulness and analytical value.
What is Pseudonymization in Data Security?
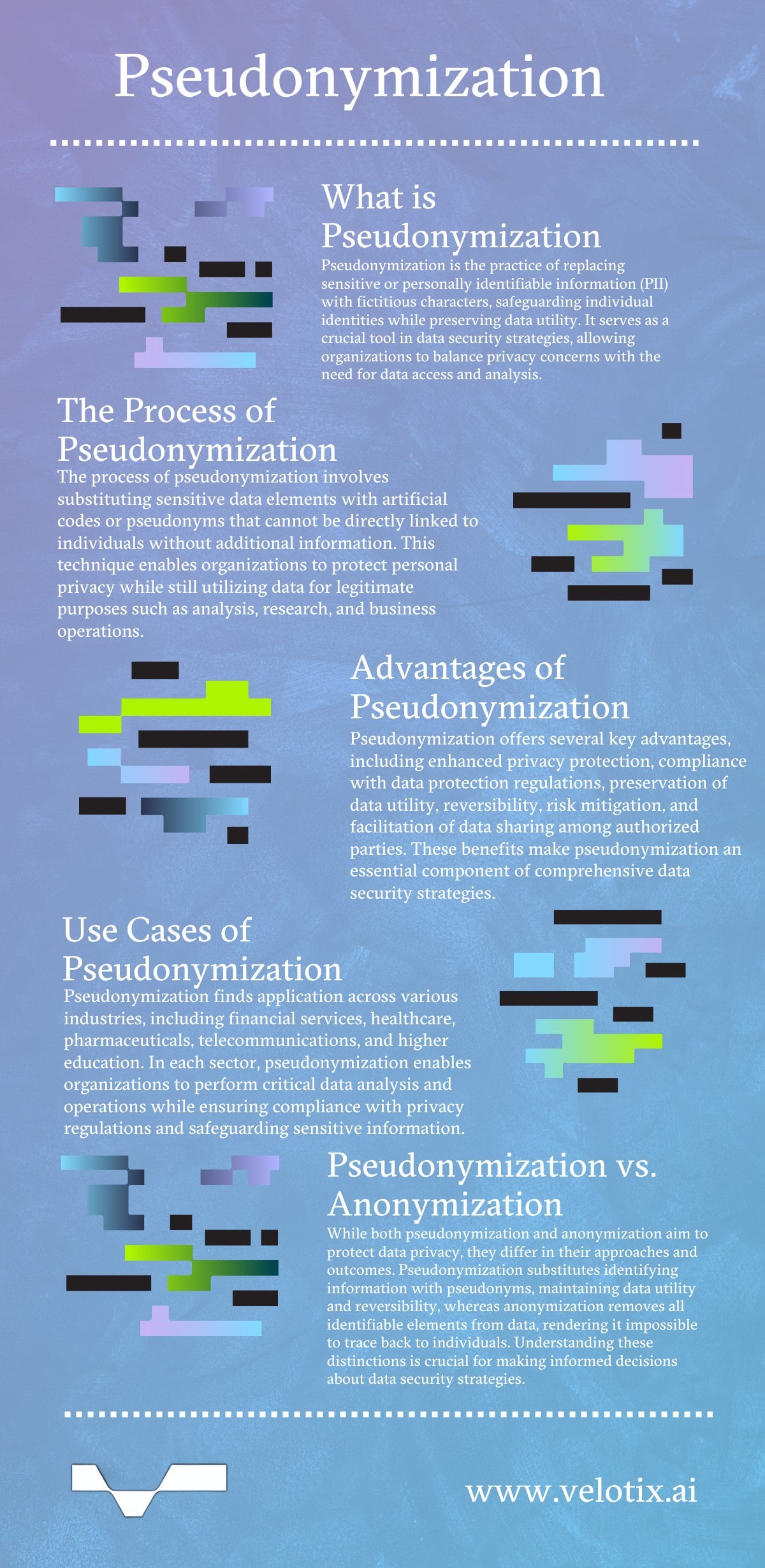
A pseudonym is a fictitious name that’s used instead of a person’s actual name. In data security, pseudonymization replaces sensitive or personally identifiable information (PII) with fictitious characters, “masking” individual identities. It allows organizations to safeguard user privacy while still being able to access and use the data for business purposes.
Organizations worldwide and across various industries use pseudonymization as part of their data protection and compliance strategies. Data pseudonymization tools help businesses strike a balance between privacy and utility, making them a vital component of robust data governance and security practices that are compliant with various data protection regulations.
The Process of Pseudonymization
The data pseudonymization process substitutes sensitive or identifying data elements like names, addresses, and social security numbers with artificial codes or pseudonyms that can’t be directly linked to an individual without additional information. Its primary goal is to safeguard personal privacy while enabling organizations to continue using their data for legitimate purposes, such as analysis, research, or business operations.
Pseudonymization plays a critical role in enabling data sharing and collaboration while upholding privacy standards. By replacing sensitive information with pseudonyms, enterprises can share data with authorized third parties, including research institutions and business partners, without compromising individual privacy. This facilitates data exchange and fosters innovation, as pseudonymized datasets can be analyzed and used for various purposes without exposing personal identities.
The process incorporates several approaches, including:
- Deterministic pseudonymization uses a predetermined algorithm or function to consistently replace sensitive data elements with the same pseudonym each time, ensuring consistency and enabling data matching across multiple datasets.
- Randomized pseudonymization replaces sensitive data with randomly generated pseudonyms, making it more difficult to link the pseudonymized data back to the original identities while also preventing data matching across different datasets.
- Tokenization substitutes sensitive data with non-sensitive placeholders or “tokens” that have no inherent meaning, effectively masking the original information while preserving its format and length.
- Format-preserving pseudonymization replaces sensitive data elements with pseudonyms that maintain the data’s original format and structure. Examples include preserving the length and character composition of credit card numbers or social security identifiers.
Each of these data pseudonymization techniques provides companies with various options to protect sensitive information while enabling legitimate data processing and analysis, striking a balance between privacy and utility. Implementing robust pseudonymization protocols is a crucial step in ensuring compliance with data protection regulations and safeguarding individual privacy.
Advantages of Pseudonymization
Pseudonymization enables organizations to balance the need for data protection and privacy with the ability to leverage data for legitimate purposes, making it an essential component of a comprehensive data security strategy.
Key benefits include:
- Enhanced Privacy Protection. By replacing PII with pseudonyms or artificial identifiers, pseudonymization masks individual identities, reducing the risk of unintended disclosure or misuse of sensitive data.
- Compliance with Data Protection Regulations. Many global data protection laws and regulations, including the GDPR, CCPA, and HIPAA, recognize pseudonymization as an acceptable method for protecting personal data and meeting regulatory requirements.
- Data Utility Preservation. Unlike complete anonymization, which can reduce data’s value for analysis, pseudonymization maintains data integrity and usefulness by preserving the relationships and patterns within the dataset.
- Reversibility. Pseudonymization is a reversible process, meaning original identities can, if necessary, be restored under appropriate controls and with proper authorization. This flexibility allows organizations to respond to legal or operational requirements while ensuring data protection during regular operations.
- Risk Mitigation. Implementing pseudonymization allows organizations to reduce the risk of data breaches and unauthorized access to sensitive information, minimizing the legal liabilities, financial penalties, and reputational damage often associated with privacy violations.
- Data Sharing Facilitation. Pseudonymized data is easier to share among authorized parties such as researchers, collaborators, and third-party service providers while still maintaining data privacy and adhering to regulations.
Use Cases
While pseudonymization techniques offer numerous advantages across various domains, specific use cases in different industries highlight this data protection approach’s versatility.
- Financial Services. Financial institutions can perform analytics, risk assessments, and fraud detection while maintaining client privacy and complying with regulations like GDPR and CCPA.
- Insurance & Healthcare. Pseudonymization protects patient, policyholder, and electronic health record (EHR) data, allowing providers to conduct research, develop personalized plans, and enhance patient care without compromising personal information, aligning with HIPAA and other privacy laws.
- Pharma/Biotech. Pseudonymization safeguards patient data in clinical trials and research, enabling companies to analyze patient outcomes and drug efficacy while ensuring confidentiality and compliance with ethical and regulatory standards.
- Telecommunications. Telecom companies can analyze customer usage patterns, improve network performance, and offer personalized services, all while ensuring customer privacy and compliance.
- Higher Education. Educational institutions can protect student data while conducting academic research, tracking performance, and personalizing learning experiences while remaining in compliance with FERPA and other privacy regulations.
Pseudonymization vs. Anonymization
Pseudonymization and anonymization each offer data security, privacy protection, and compliance. However, the two approaches differ in one significant way:
- Anonymization removes the possibility of identification entirely. It irreversibly strips sensitive data of any identifiable elements, rendering it impossible for anyone — including whoever controls the data — to trace the information back to a specific individual. This comprehensive removal of identifying details from datasets deems the anonymized data outside the scope of data protection regulations, as it no longer constitutes PII.
- Pseudonymization balances privacy and data utilization. It takes a different approach, substituting identifying information within a dataset with pseudonyms or artificial identifiers. While the original data might still be indirectly linkable to an individual, accessing it requires additional, separately stored information or “keys.” This extra protection layer segregates sensitive details from the pseudonyms and creates a barrier that makes it more challenging for anyone to identify individuals from the pseudonymized data. Pseudonymized information is still considered personal data because it can be reversed and linked to specific individuals.