Third-party cookies have been in use since Netscape invented them in 1992. Most experts credit them with the incredible growth of the digital advertising industry, which is now worth over $600 billion. As third-party cookie use declines due to privacy concerns and laws like the GDPR, enterprises are looking for alternative ways to maintain customer privacy while maximizing customer data use.
Data clean rooms let organizations share data safely and securely while staying compliant.
What is a Data Clean Room?
Data clean rooms are secure and controlled environments for the safe handling, analysis, and processing of data. They ensure data integrity, privacy, and a “contamination-free” space where data can be retrieved and used without the risk of unauthorized access or breaches, helping address major concerns related to data privacy, security, and regulatory compliance.
A data clean room facilitates collaboration on data-driven projects without users directly sharing sensitive information. Organizations can use the room to pool, analyze, and derive insights from stored data, all while ensuring raw datasets remain invisible and inaccessible to external parties.
A significant application of data clean room technology is clean room data recovery. The process involves retrieving data from damaged or failed storage devices within a controlled environment where air is filtered to eliminate microscopic dust particles and other contaminants that often make their way into hard drives.
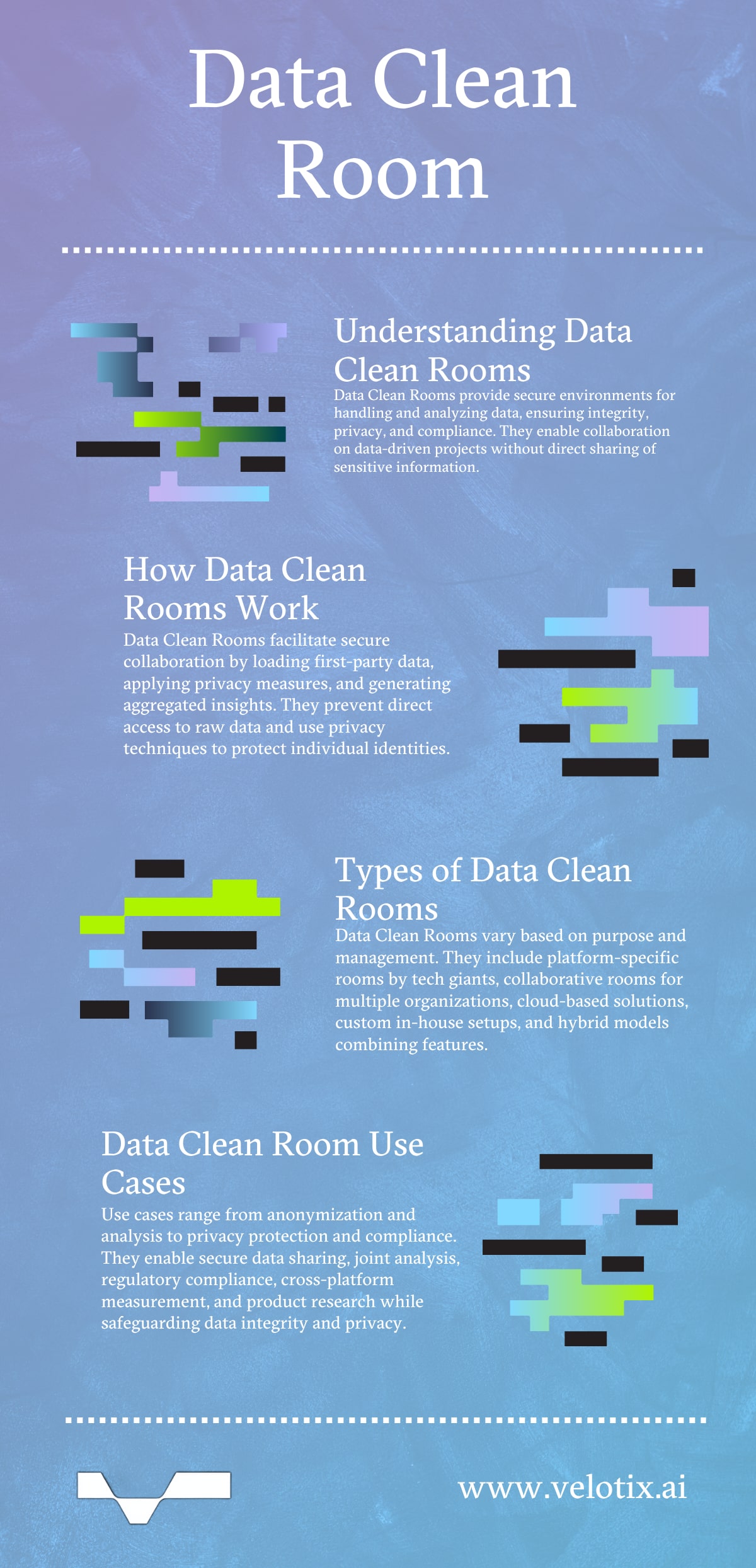
How Does a Data Clean Room Work?
Data clean rooms enhance privacy, security, and regulatory compliance in data analysis and collaboration. They operate as intermediary zones where two or more datasets “meet” to be analyzed and computed without ever merging or being exposed to each other.
The first step involves “loading” first-party data to the data clean room, followed by “cleaning,” or the applying of various security and privacy protection measures, such as pseudonymization and restricted data. The final step is “ready to use” or data cleansed reports, which can be analyzed for other activities.
- The process begins when collaborators decide to work together. Each party uploads its dataset into the clean room; however, algorithms, queries, and computations run on the datasets in the clean room ensure that each party’s raw data is not directly shared with any other party.
- As security is paramount, the clean room’s infrastructure is designed to prevent any direct access to raw data; only aggregated results or insights can be viewed. For instance, if two enterprises want to understand a concept like audience overlap, the clean room will indicate a percentage figure but won’t reveal the specific individuals that overlap.
- Different privacy techniques are used to ensure any analysis results cannot be used to infer specifics about an individual.
- Rules and permissions that dictate what type of analysis can be done, by whom, and to what extent are set within the clean room.
Types of Data Cleaning Rooms
There aren’t strictly defined types of data clean rooms, but they can be categorized based on their purpose, functionality, or whoever creates and manages them. Some distinctions between various data clean room solutions include:
- Platform-specific clean rooms. Major tech platforms like Meta (Facebook), Google, and Amazon have developed their own data clean rooms (walled gardens), which allow advertisers to match their data with platform user data.
- Collaborative clean rooms, which allow two or more organizations to work together on data-driven projects. These clean rooms are particularly useful when competitors work together but don’t want to expose trade secrets.
- Cloud-based clean rooms. Many businesses are now leveraging cloud platforms to create data clean rooms. They appreciate the flexibility and scalability the cloud offers, as it easily adapts to varying volumes of data and computational needs.
- Custom in-house clean rooms are often developed by larger enterprises with the resources to tailor them to their specific needs. They’re created and managed on-premises, offering a customized environment that aligns with an organization’s unique data requirements and privacy policies.
- Hybrid clean rooms combine the features of platform-specific and custom in-house clean rooms. They’re often established in collaboration with third-party platforms.
- Clean rooms for data recovery. While not directly related to digital advertising or marketing, clean rooms in data recovery ensure no contaminants harm sensitive storage device components during a recovery process.
Data Clean Room Use Cases
Common use cases for data clean rooms include:
Anonymization
Organizations often possess sensitive information that, if exposed, could violate privacy regulations. A data clean room ensures raw data is processed and anonymized without revealing individual identities. Typical anonymization methods include encryption and hashing.
Analysis
Enterprises can collaborate on data-driven projects, pooling their data and making joint analyses without revealing the raw data of each party. One of the most well-known analysis use cases for data clean rooms is customer lifetime value (CLV), which lets organizations make user-level analyses of customers across multiple metrics while maintaining user anonymity.
Privacy
Clean rooms use automated solutions to protect individual user data without sacrificing effective privacy. For example, when enterprises want to merge datasets for better audience targeting, they can use a clean room to view segments of interest without exposing personal user details.
Compliance
Regulatory compliance, especially in the finance and healthcare sectors, is crucial. A clean room helps institutions share and analyze data while staying compliant with industry, state, and federal regulations.
Other use cases include cross-platform measurement, where brands can use clean rooms to gauge the collective impact of their marketing campaigns, and product research and development, where external data can be analyzed while data security and integrity are left uncompromised.